Analysis of the Effectiveness of Security Information and Event Management (SIEM) Detection Against Advanced Threats
DOI:
https://doi.org/10.38035/gijes.v3i3.849Keywords:
SIEM, Advanced Threat Detection, APT, CybersecurityAbstract
Advanced Persistent Threats (APTs) pose a serious challenge to information systems security. APTs employ complex and persistent techniques to achieve their goal of infiltrating an organization’s network. APTs often operate undetected for prolonged periods, which can last months or even years. The combination of intricate techniques and long-term persistence is what makes APTs so difficult to detect and counter. Security Information and Event Management (SIEM) is a type of security solution used for cyber threat detection and response. This research analyzed the effectiveness of SIEM in detecting APTs based on parameters such as detection speed, accuracy, and false positive rate. Simulations of repeated attacks demonstrate that SIEM expands security visibility and enhances the network’s ability to respond to attacks rapidly. However, large log volumes present a challenge to the entire system, and optimal configuration incurs a high cost for such analysis.
References
Abdulhammed, R., Faezipour, M., Abuzneid, A., & AbuMallouh, A. (2021). Deep and machine learning approaches for anomaly-based intrusion detection of imbalanced network traffic. IEEE Sensors Letters, 5(1), 1–4.
Alzahrani, A., & Aldhahri, E. (2021). A machine learning approach for security information and event management. International Journal of Advanced Computer Science and Applications, 12(6), 108–115.
Bhatt, S., Manadhata, P. K., & Zomlot, L. (2014). The operational role of security information and event management systems. IEEE Security & Privacy, 12(5), 35–41.
Bilge, L., & Dumitras, T. (2012). Before we knew it: An empirical study of zero-day attacks in the real world. Proceedings of the 2012 ACM Conference on Computer and Communications Security (CCS), 833–844.
Chen, P., & Hutchins, E. (2014). Advanced persistent threat. International Journal of Computer Science and Information Security, 12(9), 1–9.
Chuvakin, A., Schmidt, K., & Phillips, C. (2013). Logging and log management: The authoritative guide to understanding the concepts surrounding logging and log management. Syngress/Elsevier.
Ferrag, M. A., Maglaras, L., Moschoyiannis, S., & Janicke, H. (2020). Deep learning for cyber security intrusion detection: Approaches, datasets, and comparative study. Journal of Information Security and Applications, 50, 102419.
Hidayat, R., & Santoso, B. (2021). Analisis manajemen respons insiden keamanan siber pada sektor perbankan Indonesia. Jurnal Keamanan Informasi dan Siber, 3(1), 22–30.
Hutchins, E. M., Cloppert, M. J., & Amin, R. M. (2011). Intelligence-driven computer network defense informed by analysis of adversary campaigns and intrusion kill chains. Leading Issues in Information Warfare & Security Research, 1(1), 80–106.
Kurniawan, Y., & Firmansyah, D. (2022). Analisis keamanan jaringan terhadap ancaman siber pada infrastruktur teknologi informasi. Jurnal Keamanan Siber Indonesia, 2(1), 14–22.
Lestari, D., & Wijaya, R. (2022). Pemanfaatan intelijen ancaman siber dalam sistem deteksi intrusi berbasis machine learning. Jurnal Teknologi dan Sistem Informasi, 8(2), 55–63.
Miloslavskaya, N., & Tolstoy, A. (2016). Big data, fast data and data lake concepts. Procedia Computer Science, 88, 300–305.
Nugroho, A., & Pratama, I. (2021). Penerapan intelijen ancaman siber untuk mitigasi risiko keamanan informasi organisasi. Jurnal Ilmu Komputer dan Informatika, 7(1), 44–52.
Prasetyo, D., & Nugroho, A. (2022). Implementasi manajemen respons insiden keamanan siber pada organisasi pemerintah. Jurnal Sistem Informasi dan Teknologi, 4(1), 33–41.
Pratama, I. P. A. E. (2021). Keamanan sistem komunikasi data pada jaringan komputer. Jurnal Ilmu Komputer dan Informatika, 7(1), 55–63.
Rahayu, S., & Prasetyo, A. (2021). Implementasi prinsip CIA dalam sistem keamanan informasi perusahaan. Jurnal Informatika dan Komputer, 8(1), 12–19.
Ramadhan, F., & Fauzi, A. (2023). Strategi intelijen ancaman siber dalam menghadapi advanced persistent threat pada infrastruktur kritis. Jurnal Keamanan Siber Indonesia, 4(1), 10–18.
Rid, T., & Buchanan, B. (2015). Attributing cyber attacks. Journal of Strategic Studies, 38(1–2), 4–37.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2025 Dilla Ghaisani Putri

This work is licensed under a Creative Commons Attribution 4.0 International License.
Copyright:
Authors who publish their manuscripts in this journal agree to the following conditions:
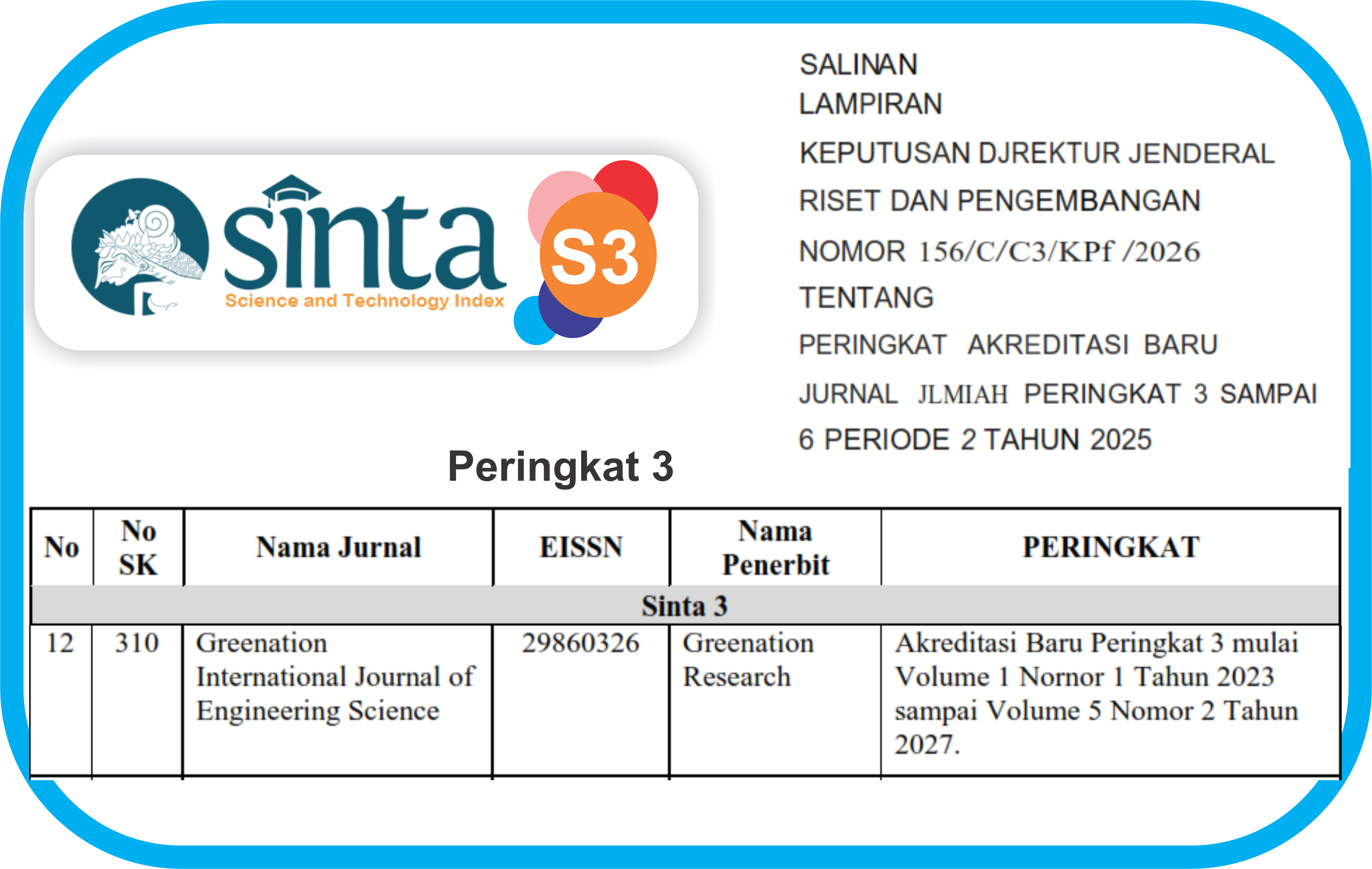
- Copyright in each article belongs to the author.
- The author acknowledges that Greenation International Journal of Engineering Science (GIJES) has the right to be the first to publish under a Creative Commons Attribution 4.0 International license (Attribution 4.0 International CC BY 4.0).
- Authors can submit articles separately, arrange the distribution of non-exclusive manuscripts that have been published in this journal to other versions (for example, sent to the author's institutional repository, publication in books, etc.), acknowledging that the manuscript has been published for the first time in GIJES.